Geek Stuff category archive
The Disinformation Superhighway 0
At Psychology Today Blogs, Stacey Woods offers some tips to avoid being taken in by scams on “social” media.
It’s required reading, because, as has been so often demonstrated, “social” media isn’t.
The Search for the Scream 0
Yesterday, I climbed my stairs and heard a high-pitched screaming sound that came from I knew not where, but it seemed to be coming from my room.
I entered my room, but could not locate its source. It seemed to come from everywhere.
I went to the breaker box and opened the breaker for my room and the sound went away, proving it came from my room.
I closed the breaker and the sound came back, still seeming to come from everywhere.
Twits Own Twitter X Offenders
0
Above the Law reports that Elon Musk seems ill-deposed.
Quality Construction at a Price that Frights 0
Emma and the crew discuss some issues encountered by persons who have purchased Tesla Cybertrucks and later discovered that they were well and truly trucked.
Also, too . . . .
Aside:
I happen to know someone who owns a Tesla.
I asked him about Tesla’s “autopilot.” He told me it was like an enhanced cruise control that could, for example, sense when cars ahead were slowing down and react accordingly.
I asked him if he ever read a book while he was on “autopilot.”
He said, “No.”
No doubt because he’s sane.
Twits Own Twitter X Offenders
0
Elon Must styles himself as a “free speech absolutist” (unless, of course, someone tweets–or is it now Xcretes?–something with which he disagrees).
Au contraire, says the editorial staff of the Las Vegas Sun, which argues forcefully that Musk does not even understand what “freedom of speech” means.
Geeking Out 0
One of my computers died after long and faithful service, so I’ve been having fun tweaking my new one, which I ordered with the Debian Linux OS and the Plasma desktop environment. In a few more days, I’ll have it set up to my satisfaction. In the meantime, I’ve others to use, as the Going Linux guys say, to get stuff done.
I must say, I was somewhat taken aback. I ordered it Sunday night and it arrived, configured to my specifications, on Wednesday, much earlier than I expected.
The Crypto Con 0
Yes, indeedy-do, it seems that there’s an app for that.
Driven to Destruction 0
The other day, I had a very scary experience.
I was behind a Tesla with a little bumper sticker that said, “I’m probably on autopilot.”
I’m just glad I wasn’t in front of it.
It’s All about the Algorithm 0
At Psychology Today Blogs, Christine Louise Hohlbaum discusses David Donnelly’s documentary, The Cost of Convenience, which explores the extent to which corporate digital surveillance has been woven into our society and economy. Here’s an excerpt:
She ends the article with some suggestions as to how to fight back.
Me, I’m going to keep an eye out for the film.
Twits Own Twitter X Offenders
0
San Francisco judge dismisses Elon Musk’s empty suit.
Some of the judge’s comments, as quoted in the news story, delight the soul.
Much Ado about Not Much of Anything:
What Drives Drivel on the Disinformation Superhighway
0
I found the recent recent who-shot-john about Princess Kate to be–er, what’s the word I’m looking for?–stupid. Here’s a person who’s in the public eye only because of whom she’s married to, and who she’s married to is in the public eye only because he’s descended from folks who use to rich, influential, and powerful, persons who are now rich and not very influential (and, to the extent they are influential, they choose not to exercise influence, for fear the hollowness thereof will be exposed). Yet, persons spent a week or more speculating, questioning, and conspiracy theorizing on “social” media because she had not been seen in public for a couple of months.
At Psychology Today Blogs, Susan Albers takes a look at the the dynamics that powered this spectacular waste of time and energy, concluding that
Methinks her article is worth a read, as it sheds some light on how and why falsehood, irrelevance, and just plain stupid jams up the disinformation superhighway.
Shotspitter 0
The EFF has long warned of the dangers of certain technologies with which law enforcement seems enamored, such as shotspotter and facial recognition. Here’s a bit from their latest article on the topic:
In a subsequent assessment of the event, the Chicago Civilian Office of Police Accountability (“COPA”) concluded that “a firearm was not used against the officers.” Chicago Police Superintendent Larry Snelling placed all attending officers on administrative duty for 30 days and is investigating whether the officers violated department policies.
Follow the link for context.
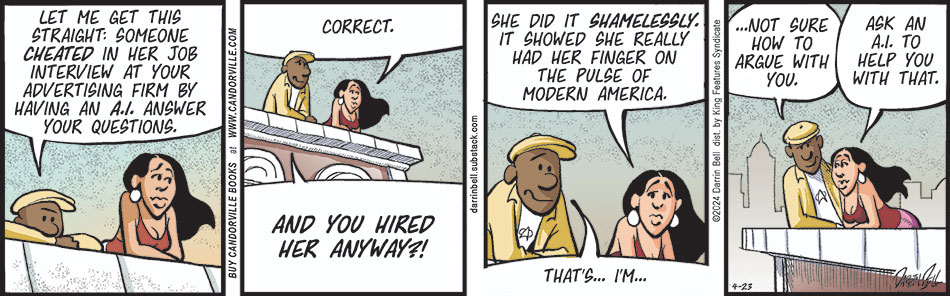
Artificial? Yes. Intelligent? Not So Much. 0
Also, not your friend despite what they want you to think, as sociologist Joseph E. Davis points out at Psychology Today Blogs, where he points out that
Follow the link for the evidence.
If One Standard Is Good, Two Must Be Better, Disinformation Superhighway Dept. 0
The EFF’s David Greene highlights the hypocrisy, A snippet:
Agencies can’t even pass on information about websites state election officials have identified as disinformation, even if they don’t request that any action be taken, they assert.
Yet just this week the vast majority of those same lawmakers said the government’s interest in removing election interference misinformation from social media justifies banning a site used by 150 million Americans.
Details at the link.